Category: privacy
-
Why I am not switching browsers
Recently, there have been many new browsers that are just forks of the Chrome browser technology. And then they just added skin on top of it and add a layer of AI. Here are the reasons why I am not going to install another browser.
-
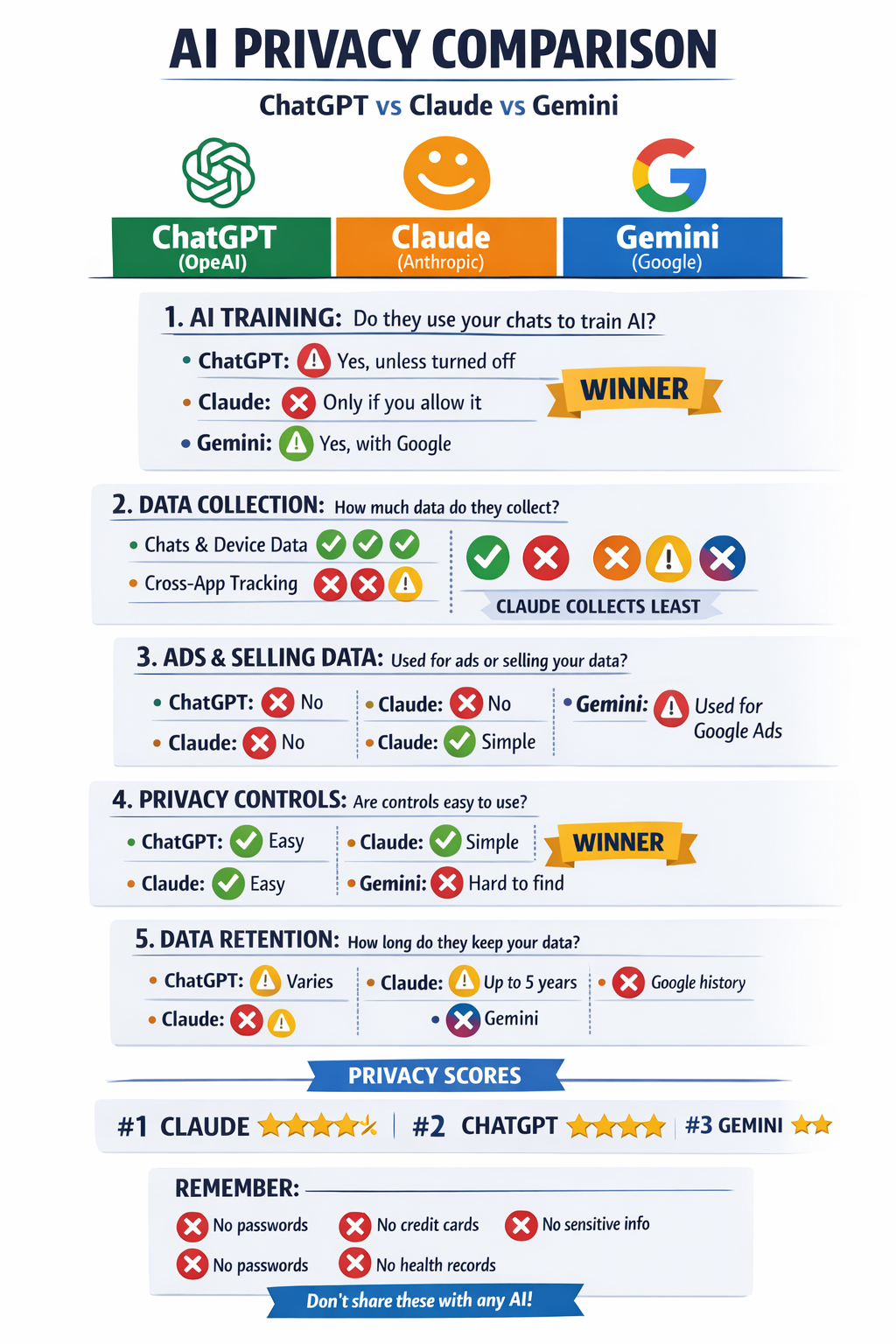
If Data Privacy Is Important to You.. which AI do you choose?.
Even when you pay for products such as ChatGPT, Anthropic, Gemini, your user data is still being used to train AI or other products. Try asking the following of your favorite AI. Generate an info graphics that is easy to read, who the winner is, to compare the privacy policies of the following. The output…
-
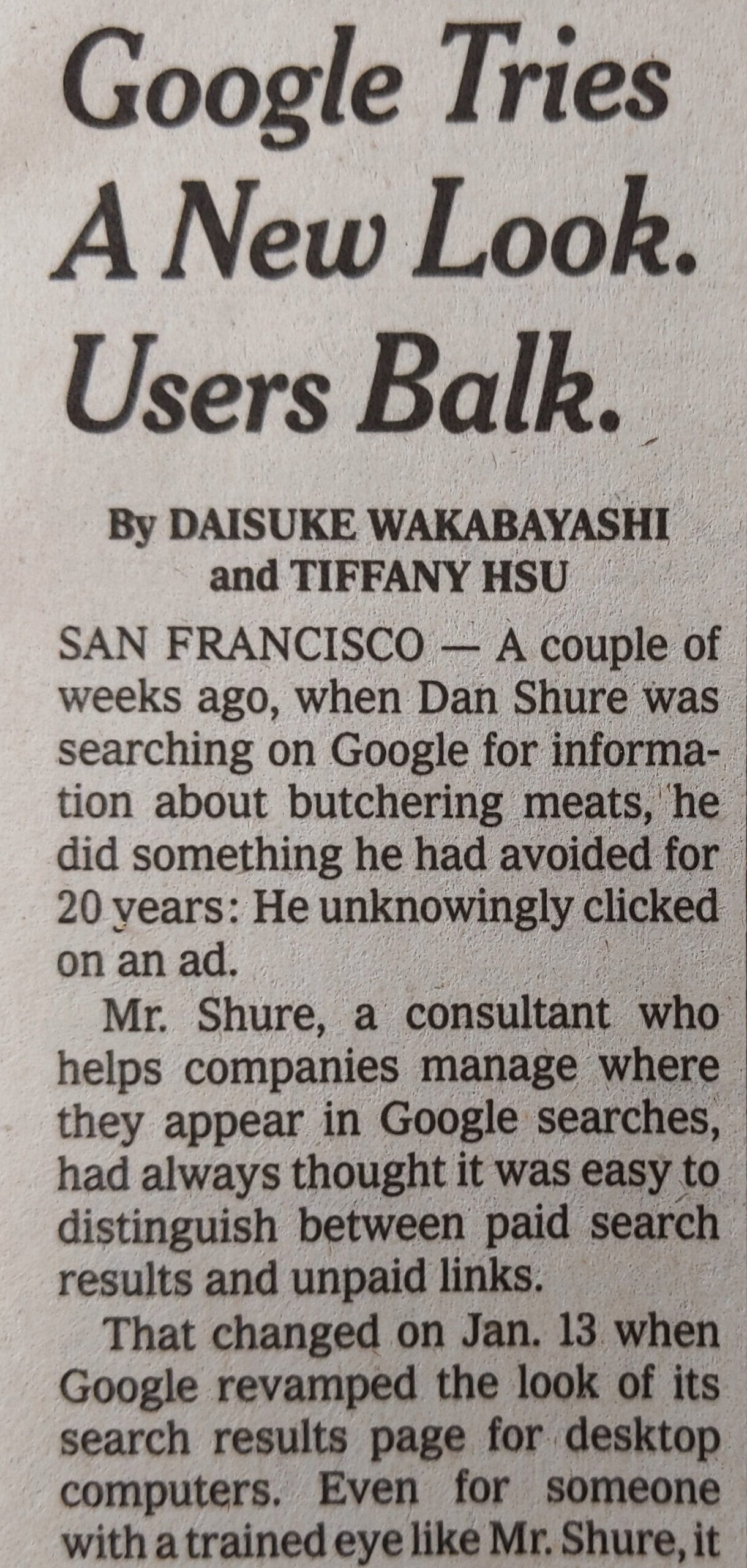
Don’t fight Google Search, switch to DuckDuckGo
-

Be onguard about your data with anything on Facebook
Wednesday’s report from TechCrunch of an “exposed server” that “contained more than 419 million records over several databases on users across geographies, including 133 million records on U.S.-based Facebook users, 18 million records of users in the U.K., and another with more than 50 million records on users in Vietnam.”
-

Skin in the game: regulation vs. being sued
Take a company like Facebook. They leave millions of passwords in plain text, they created the news feed where dictators use the various Facebook products (Instagram, FB, Whatsapp) to spread fake propaganda, they violate our privacy repeatedly (even those of us who don’t use it, but are connected to people who do) and hijack our…
-

Link NYTimes: I Deleted Facebook Last Year. Here’s What Changed (and What Didn’t).
I also deleted Facebook, stop using any apps that are personalized infinite scroll apps, but did not add tracker blocker. It is interesting to see this person actually bought less online as a result of not getting personalized ads. I Deleted Facebook Last Year. Here’s What Changed (and What Didn’t). https://nyti.ms/2YdvvKk
-

You leak my data, 1 strike and you are out!
Goodbye Quora, you leak my data and I delete my account on your services. Goodbye Yahoo, you leak my data and I delete my account. Anyone else?
-
If you want true privacy, do not use your mobile phone
(The photo is of my sister and I in China 1975) I was listening to Leo Laporte’s Tech Guy podcast and he was commenting on the FBI vs Apple case about unlocking an iPhone used by the the shooters. He was pointing out the following misconceptions in the popular press. Inspired by his comments about…
-
5 Simple Steps To Securing Your Online Privacy And Security In 2016
Do you have the same password for multiple online accounts? Imagine the worst case senario that can happen if any of your accounts were hacked. These types of accounts are a nightmare if they were hacked: your email, Apple account, bank account, LinkedIn, Facebook, twitter. You could be publicly embarrassed, financially compromised or worst, compromise…